Breach after breach has shown that IT asset disposition is a blind spot. The Defensible Asset Disposition Framework gives CISOs a way to close the gap and stay compliant with ISO 27001 and SOC 2.
Certification vs Verification in ITAD
Certification in ITAD proves vendor credibility, while verification ensures ongoing compliance. Veridy Verification enhances security, addressing gaps like theft detection.
USAID’s Reckless ITAD Gamble
Federal Agency takes risky ITAD gamble with remote wiping. Fired USAID workers will have to dispose of laptops, iPhones, and iPads on their own.
3 Myths About Fixing Bad ITAD
ITAD fears costing you? Debunk 3 myths! Fixing IT asset disposition is simpler, cheaper, & less disruptive than you think. Protect data, ensure compliance. Read why!
ITAD Asbestos
CISO Alert: Don’t let ITAD blind spots become a career-ending SEC fine. Neglected IT disposal creates hidden vulnerabilities that regulators now call willful negligence.
CISO Guide to ITAD
CISO Alert: Don’t let ITAD blind spots become a career-ending SEC fine. Neglected IT disposal creates hidden vulnerabilities that regulators now call willful negligence.
10 “Astonishing” Facts about Morgan Stanley’s ITAD Blunder
Morgan Stanley’s ITAD blunder: $161.5M in fines. SEC lists 10 “astonishing” facts—lost servers, epic fails. Trust trashed.
Almost Everything You Think About ITAD is Backwards
Almost everything about ITAD is backwards. Trusting the same people to track and retire assets, consolidating vendors, and prioritizing cost court disaster.
Driver Theft in ITAD
Driver theft in ITAD risks huge losses and noncompliance, but segregation of duties, disposal tags, and verification holds can secure the process.
What is Defensible IT Asset Disposition?
Defensible IT asset disposition (ITAD) is a strategic approach that aligns an organization’s ITAD program with business objectives, regulations, and risk mitigation.
Gartner Bombshell: 30% of IT Assets Lost
Gartner’s new report is a bombshell: 30% of IT assets are lost or unaccounted for. This is a major cybersecurity security risk that most organizations are ignoring.
The Importance of Records Reconciliation in IT Asset Disposition
The SEC is serious about cybersecurity, and they expect companies to have a secure and compliant ITAD process. Records reconciliation isn’t an option—it’s mandatory.
The Lifeguard and ITAD Governance: Why Silence is the Scariest Sound
Lifeguards have a saying: You worry less about the screaming kids and more about the ones who are eerily quiet. Successful ITAD is not silent. The red flag goes up when things get too quiet.
Cybersecurity’s B.I.G. Problem: Bad ITAD Governance
Non-compliant IT asset disposition (ITAD) is a major cybersecurity risk. The “BIG Problem” refers to “Bad ITAD Governance,” where missing equipment and conflicts of interest create security vulnerabilities.
Understanding the Difference Between ITAD Consultants and Service Providers
Traditional ITAD vendors can undervalue equipment & lack transparency. Learn how ITAD consultants offer a secure, cost-effective solution with maximized value recovery.
From Niche to Necessity: The Future of IT Asset Disposition Safeguards
By implementing three safeguards (segregation of duties, disposal tags, and equipment verification holds), your organization can safeguard against non-compliant ITAD.
Where the IT Lifecycle Ends
You can’t solve a problem you can’t discuss. This book uses cartoons to expose the hidden dangers of bad ITAD and shows you how to talk about it (before it’s too late!).
Why Hardware Asset Management is Harder Than Accounting
Struggling to keep track of your laptops? Turns out, hardware management is like herding cats compared to accounting. Dive in for the hilarious & frustrating world of HAM!
Why Recusal is Crucial for Responsible Asset Disposition
IT asset managers must stop juggling both lifecycle and disposal! It’s a recipe for data breaches and compliance woes. Segregation of duties is required for clear accountability, compliance, and ethical practices. Don’t be the fox guarding the hens!
The IT Asset Houdini Act
In the world of IT asset management, assets disappear like magic. But when it’s time for retirement, they reappear. However, this isn’t magic; it’s smoke and mirrors. Learn how Retire-IT brings clarity and SEC compliance to ITAD.
ITAD Isn’t Just Disposal; ITAD is Cybersecurity
IT Asset Disposition (ITAD) is not just about getting rid of old devices; it’s a critical part of cybersecurity. Ignoring ITAD can lead to data breaches and regulatory non-compliance.
The Crucial Role of Exception Reports in ITAD Management
Exception reports are crucial for ITAD management as they highlight deviations from established procedures and help identify missing assets. Without them, organizations are left to hope for the best, leaving their security posture vulnerable.
Morgan Stanley’s Data Breach That Won’t Die
Morgan Stanley faces continued scrutiny for its mishandling of IT asset disposal, leading to a $161.5 million penalty and raising concerns about its ITAD management practices.
Disposal Tags are Damage Control
Disposal tags are an essential tool for ITAD, providing instant chain of custody, theft deterrence, and discreet problem handling.
Equipment Verification Holds: A Crucial Safeguard in IT Asset Disposition
Among the many ITAD practices, Equipment Verification Holds stand out as a fundamental safeguard and they should never be overlooked.
The Flawed ITAM Paradigm
Summary of IAPP article explains ITAM/ITAD conflict of interest risks privacy and cyber security. SEC regulations require SOD.
Data Destruction Alone Won’t Cut It
Pre-disposal data protection is vital, but not enough. Comprehensive safeguards are essential to prevent data breaches.
SEC Interest in Toxic IT Assets
The SEC now requires disclosure when a string of cybersecurity incidents becomes material. Together, toxic IT assets pose a major concern.
What the SEC’s Cybersecurity Whistleblower Program Means to ITAD
The SEC’s cybersecurity whistleblower program means an organization’s IT asset disposition (ITAD) program is just two clicks away from being exposed.
Why You Can’t Count On Cyber Liability Insurance To Cover An ITAD Data Breach
If you think your cyber insurance claim will protect you from an IT asset disposition (ITAD) incident, it’s time to think again. Hidden in the fine print are certain terms and conditions you must comply with.
What We Learned from The Morgan Stanley Breach
Morgan Stanley’s recent slipup with ITAD cost them $60 million in fines and another $60 million to settle a class-action lawsuit. What are the two key lessons we can draw from the Morgan Stanley breach?
How the Zero-Trust Model Helps IT Asset Managers Protect Their Organization (And Their Jobs)
Zero-Trust is a must for network access and it should extend to your decommissioned IT assets. After all, if you can’t trust devices while they’re on your network, why would you trust them after they’ve been disposed of?
Box Cutters Don’t Bring Down Buildings
The tragedy of 9/11 taught us not to disregard security threats or underestimate bad guys. ITAD is a disregarded cybersecurity threat. If we fail to imagine what could happen, we risk repeating the same mistake.
The Zero-Trust ITAD Framework: 4 Ways to Protect Your Company’s Data Security
The Zero-Trust security model has gained acceptance as the go-to framework for network security. But Zero-Trust isn’t just effective in combating modern cyber threats; it’s also the cornerstone of an effective IT asset disposition strategy.
The Five Most Common ITAD Mistakes (And How to Avoid Them)
Learn about the five most common ITAD mistakes and how to avoid them. When an organization fails to manage ITAD effectively, it becomes exposed to legal risks, environmental concerns, and unnecessary costs.
Toxic IT Assets (And How to Eliminate Them)
Unwanted IT assets become toxic when they go missing. This is usually due to loss or theft. However, the most common culprit is apathy. Companies that fail to make ITAD a priority put themselves at the greatest risk of losing valuable assets.
What the Debate Around Face Masks Has Taught Us About Disposal Tags
Disposal tags don’t save lives, but they are a critical tool for making IT asset disposition (ITAD) safe and effective. However, there are still naysayers out there who claim the costs aren’t worth the benefits.
3 Reasons Why Disposal Tags Are the Best Security Decision You’ll Ever Make
Executives must make tough decisions. Disposal Tags are the easiest decision you will ever have to make because they maintain accountability and offer multiple solutions in one simple package.
Data Breach Prevention Driver for Disposal
Headline-grabbing news of privacy breaches has fueled increased interest in GRC initiatives. IT asset managers have an opportunity to demonstrate value and elevate their profession.
Disposal Tags are Hands-Only CPR for Your ITAD Program
ITAD can be intimidating, just like CPR. And while disposal tags don’t save lives, they can save your company from catastrophic data breaches.
Why Caring About ITAD Matters to Your Employees
Not prioritizing ITAD at the executive level is understandable. However, when your employees and vendors disregard proper protocols, that’s a different story.
Identifying the Best (And Worst) ITAD Vendors for Your Business
Level the playing field and optimize ITAD results with a new multi-vendor approach. Achieve ITAD by making money from equipment while minimizing freight, fees, and environmental impact.
The Importance of Disposal Tags
Disposal tags are your company’s weapon in the fight against data breaches. Retire-IT looks out for you and your team by supplying tags for your expired assets before they ship.
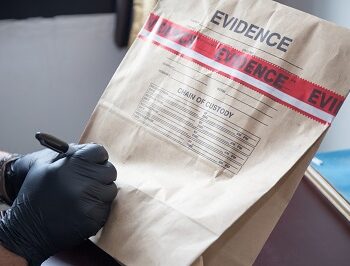
What is Chain of Custody?
Understanding the chain of custody process is critical to the protection of your company’s assets. This includes documenting when it was collected, where it was transferred, and who handled it.
Democratizing ITAD
Level the playing field and optimize ITAD results with a new multi-vendor approach. Achieve ITAD by making money from equipment while minimizing freight, fees, and environmental impact.
Does Morgan Stanley Hope It’s Too Small to Fail?
Morgan Stanley notified customers that a vendor failed to remove client data from hardware and it discovered old servers could not be located.
What Webvan Taught Us About Arrow’s ITAD failure
What groceries, flowers, and old computers have in common. How Webvan and Gerald Stevens forewarned us of Arrow’s foray into IT asset disposition was doomed.
Why IT Asset Managers Reject Tools
What does Modern Medicine and IT Asset Management have in common? For more than 100 years, doctors dismissed the invention of the thermometer because they feared the new technology would make their jobs obsolete.
Beware When Judge Wants ‘Bone-Crushing’ Discovery
When a Federal Judge wants ‘bone-crushing’ discovery into data breach, we are entering a new era of increased accountability which will impact IT Asset Management (ITAM) and IT Asset Disposition. Learn how to close the ITAD gap and be prepared.
What is IT Asset Disposition ITAD?
What is IT Asset Disposition? IT asset disposition, also referred to as ITAD, is the process of disposing of unwanted electronic equipment in a responsible manner. Successful ITAD programs mitigate risk, minimize cost, and maximize value recovery.
How SAM Thinking Widens the ITAD Gap
Software publishers won’t sue if you are short a license or two. When it comes to SAM and ELP, close enough is good enough. This mindset might explain why the ITAD Gap gets ignored. SAM managers must be vigilant and relearn what it means to reconcile.
Black Swan
An ITAD Black Swan is looming. We can ruin this prediction by raising awareness of the ITAD Reporting Gap vulnerability. While a Black Swan is a surprise when it occurs, experts will later conclude the event was likely. Learn how to keep your company from being one of the turkeys.
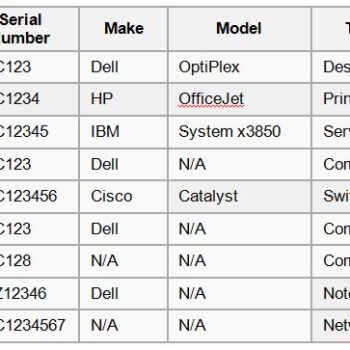
Measure the ITAD Reporting Gap in ServiceNow
ServiceNow is a fantastic tool for IT asset management. Inventory discrepancies that happen during disposal phase of the IT lifecycle represent the ITAD Reporting Gap. Here is how to use ServiceNow to measure the gap so ITAM can effectively manage and ultimately close the gap.
ITAD Reporting Gap
There comes a time in the lifecycle of every IT asset when it must retire from service. In a perfect work, ITAM should be able track 100% of assets from acquisition to disposition. We don’t live in a perfect work. The inventory discrepancies discovered during disposal phase represent the ITAD Reporting Gap.
What is Chain-of-Custody Worth?
What has more value, an armored bank truck, or a van delivering old computers to a disposal vendor? Chain-of-custody, by itself, is about as helpful as a helmet in a motorcycle crash. An effective process that prevents a disaster from happening in the first place is far more effective. Until you prove a disposal vendor has your equipment, you are responsible for it. Unless you prove it, your organization is legally exposed.
The “Golden Hour” of ITAD
There is a “golden hour” at the onset of an incident when well thought out planning and effective response can make or break the situation. Very much like in medical trauma care or criminal investigations, there is a “golden hour” of IT asset disposition (ITAD) when well thought out planning and effective response can keep an incident from becoming a costly disaster.
Disposal Tags are Like Seat Belts
Not too long ago, everyone rode bikes without helmets, no one wore seat belts, and smoking was touted as ‘good for you.’ Over time, safety data helped change public sentiment and seat belts became a standard feature in modern vehicles. Disposal tags do not save lives, but they are the most effective way for a company to safeguard itself against costly mistakes of ITAD.
Rethinking Risk for IT Asset Disposition
Today, IT asset disposition is considered low risk. Understandably, most view the chance of a retired computer causing an expensive breach as a remote possibility. ITAD is becoming a plaintiff lawyer’s dream come true, but not for obvious reasons. The biggest risk of ITAD is not data security per se. It is the governance of ITAD. Companies are unprepared to defend their ITAD programs and demonstrate their compliance with regulatory obligations.
Data Security Deserves Cyber-SOX
Love it or hate it, Sarbanes-Oxley (SOX) was enacted as a reaction to major financial scandals which shook public confidence and cost investors billions of dollars. The high-profile data security breach of Equifax has certainly shaken public confidence. The announced 143 million records compromised has prompted some to call for a “cyber Sarbanes-Oxley.” A Cyber-SOX could have similar benefits for data security that SOX had for financial security.
How to Prevent Employee Theft of Your Retired IT Equipment
As businesses struggle with strained budgets, information technology departments are becoming overworked and understaffed. This combination of factors has led to an alarming vulnerability in the security of company data resident on equipment destined for retirement. Before you dispose of IT equipment, consider these possible revisions in policy and procedures that could protect your company against data leakage.
8 Lessons Learned from 8,000 Projects
Google, “hacks to improve” and you will find a million shortcuts to improve almost any aspect of your life – your credit score, public speaking, or memory to name just a few. Finding ways to make your organization’s IT Asset Disposition (ITAD) program effective is not as easy, so we created them for you. We learned these “hacks” by studying our last 8,000 projects and observing how the most effective clients approach the management of ITAD.
Not a Faster ITAD Horse
In 1900, had Ford asked someone how to improve personal transportation, I’m sure they would have appreciated a better and faster horse. Most people could not have imagined the transportation transformation brought on by the car or airplane. Much like the cars and airplanes then, most people have not yet imagined how a multi-vendor approach can transform ITAD.
The Undoing Project, ITAD Style
I’m a fan of Michael Lewis. If you don’t know him, he’s a very talented author who is best known for The Big Short and Moneyball. His latest book, The Undoing Project, explores the extraordinary work of Daniel Kahneman and Amos Tversky. How does The Undoing Project relate to ITAD? First…
Consider ITAD a Security Threat
ITAM benefits by treating ITAD as a data security threat. Educating senior management about the risks will secure IT asset managers the resources needed to prevent an ITAD-related breach. To ensure adequate safeguards are in place, IT asset managers should consider treating ITAD as if it were an inevitable security incident.
Five ITAD Mistakes Not to Make
Organizations constantly replace outdated computers and countless types of electronic devices to keep up with technology and enhance worker productivity. This rush to upgrade, however, creates a challenge: large numbers of excess electronics must be managed and disposed of properly.
Preparing to Change ITAD Vendors
We always hope relationships will last forever in business, but that is not always the case. Anyone involved with IT asset disposition (ITAD) knows how once-trusted vendors can become unresponsive, get acquired, get into trouble, or simply go out-of-business.
The reality is, you need to be prepared at any time to switch ITAD vendors. Even if you are not forced to switch, there comes a time when change might be necessary.
My Daughter Doesn’t Get A Vote
My daughter Olivia is like most first graders. She is confident and adventurous and, at times, defiant.
When risks are low, I prefer she learn from experience. The school of hard knocks can teach valuable lessons.
When it comes to security and safety, however, the cost is too high to let her learn the hard way. As parents, we instruct but lay down the law.
Final Check-Out
How do you sum up what Retire-IT does in two words?
When I was working on this summary, I called it the “Final Check-Out.” My nine-year-old son Ryan sings it better than I can write it.
Ryan saw it and immediately asked me if it had to do with the “Final Countdown!” Remember that Swedish rock band Europe and their one-hit wonder?
College Football Resembles ITAD
What does ITAD have in common with college football? Both have a problem with players celebrating too early.
For some unexplained reason, college football players continue to drop footballs before crossing the goal line. Players from Clemson, California, Utah, and Oklahoma recently dropped the ball voluntarily before they got into the end-zone.
Your ITADs Have You By Your Assets
Your ITADs Have You By Your Assets. ITAD vendors may hide incomplete chain-of-custody info, risking trust. Protect yourself with disposal tags.
Nobody Cares About ITAD
Don’t Let Fake Recyclers Hijack Earth Day
RFP or CYA?
GTTM and ITAD
15 Minutes Could Save You $15 million
The Shameful Act of Retiring Missing Assets
Retire versus Dispose
The Preventable Breach
How Encryption Creates Vulnerability
Seven steps Coca-Cola should take to prevent another breach
Coca-Cola Should Have Prevented, Detected Disposal Breach
How To Save Your Staff 100 Hours
Prevention Is Ideal, But Detection Is A Must
Close Only Counts In Horseshoes
Why Target Is Negligent
Rules-Based Reconciliation
IT Asset Disposal Should NOT Be a Game of Chance
Corporate Cognitive Dissonance
The Right Question
Executives need to be non-credulous when it comes to ITAD reporting. Employees tend to report self-serving interpretations, especially when facts could make them look bad.
Stop Sharing
Sharing inventory with a recycler is not always a good idea, as it can lead to a false sense of security and shield the recycler from liability. Maintaining an unbroken chain of custody is crucial to hold a disposal vendor accountable.
Don’t Ruin Your Retirement
Don’t assume that your IT retirement is secure. Harvard Business Review revealed how IT asset disposition is the most overlooked aspect of data security.